
"The topics (threat modelling frameworks, zones of trust, annotating your own diagrams, implementing security into Agile practices) were all well-chosen and appropriate." GL, Software Engineer, Threat Modelling, February 2021








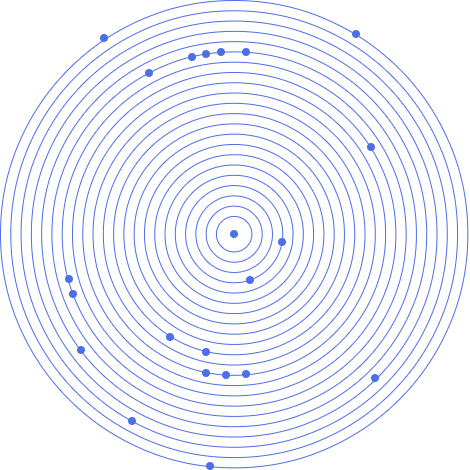
An excerpt from a 2 day JBI Threat Modelling training course showing an agile architecture session.
• The main recipients for the course are security subject-matter experts, technical non-security professionals who have no/little experience of threat modelling (e.g. software devs, architects and engineers) and technically-oriented project leaders.
• The purpose of the course is to deliver the concept of threat modelling and to be able to complete a basic threat model using the Rapid Threat Model Prototyping methodology.
• By the end of the course, the class will understand threats, mitigations and risk rankings and will be able to use basic threat modelling techniques to drastically improve secure design of software.
• The course will enable participants to integrate RTMP into any software development process.
• Overview of secure SDLC
• How Threat Modelling fits into a secure SDLC
• How Agile Architecture fits in
• Introduction to several common security classification systems
• What are STRIDE and OWASP Top 10
• Mini Lab - mapping system relationships
• Defining elements of software that are security concerns
• Threat Model types
• Traditional threat model process and its shortcomings
• The importance of context diagrams to threat modelling and reusing existing software designs
• Dependencies
• Mini Lab - discovering dependencies
• Pareto Rule (80/20 ratio) and use in secure software development
• Introduction to the Rapid Threat Model Prototyping methodology
• Elements of a threat model
• How to integrate RTMP in an Agile/DevOps process
• Zones of Trust and using Zone rules to find threats
• Adding Zone and threat metadata to a software diagram
• Mini Lab - applying Zone rules • Mitigation analysis
• Mini Lab - discovering mitigations
• Validation and triaging of results in an Agile/DevOps process
• Lab – full threat model of an internal system
• How to convert risks into backlog items that are prioritised accordingly (e.g. into Jira, MS DevOps or similar workflow systems)
• Examples and open conversation of threat models that you have from the real world, starting with simple systems and building up to more complicated systems
• How to use RTMP to quickly highlight flows/processes/etc that are high risk
• Advanced techniques using calculation of the RTMP elements. Formulae are outlined and broken down for comprehension.
• Discussion around how to implement a good security champion program to drive deep adoption of Rapid Threat Model Prototyping across the software development lifecycle.
• Use of RTMP in other parts of a business.
The main recipients for the course are security subject-matter experts, technical non-security professionals who have no/little experience of threat modelling (e.g. software devs, architects and engineers) and technically-oriented project leaders.

"The topics (threat modelling frameworks, zones of trust, annotating your own diagrams, implementing security into Agile practices) were all well-chosen and appropriate." GL, Software Engineer, Threat Modelling, February 2021
“JBI did a great job of customizing their syllabus to suit our business needs and also bringing our team up to speed on the current best practices. Our teams varied widely in terms of experience and the Instructor handled this particularly well - very impressive”
Brian F, Team Lead, RBS, Data Analysis Course, 20 April 2022

Sign up for the JBI Training newsletter to receive technology tips directly from our instructors - Analytics, AI, ML, DevOps, Web, Backend and Security.
Threat modelling is a process to identify security weaknesses in software design and architecture, and define countermeasures that mitigate the malicious effects of the discovered weaknesses before any code is cut.
Our Threat Modelling training course is designed for software developers and architects in mind. Threat modelling is language-agnostic. It can be easily used for any software development project and with any modern workflow such as Agile or DevOps. The analysis work is done on the design of the software system in order to improve the quality of the code that will be delivered in-sprint.
You will learn how to address security design concerns faced by software development teams with a combination of teaching modules and practical threat model exercises. The participants will be encouraged to work in teams, to foster discussions on how to implement security controls for the modelled threats on their software architecture.
All key stakeholders in an application development workflow should know how to assess the weak points in their systems and what questions to ask. The course will provide a framework to assess these questions and will yield immediate beneficial results.
You will gain a practical overview of the necessary disciplines for resolving application architecture and design issues according to OWASP good security practices.
We aim to instill skills that allow you to perform rapid threat modelling in a consistent, repeatable and measurable manner.
CONTACT
+44 (0)20 8446 7555
Copyright © 2025 JBI Training. All Rights Reserved.
JB International Training Ltd - Company Registration Number: 08458005
Registered Address: Wohl Enterprise Hub, 2B Redbourne Avenue, London, N3 2BS
Modern Slavery Statement & Corporate Policies | Terms & Conditions | Contact Us
POPULAR
AI training courses CoPilot training course
Threat modelling training course Python for data analysts training course
Power BI training course Machine Learning training course
Spring Boot Microservices training course Terraform training course